disclaimer: I get angry when I have to fix Windows. Expect explicit content. You have been warned.
Being computer literate can be something of a curse. Anyone with even the most rudimentary skill set has probably sometime gotten asked if they could help someone with their computer. The other day I got asked if I could help, let’s call him Roger, as he was having some problems with Windows Update. The initial symptoms could be clearly relayed by Roger:
The update gets to 30% then it just stops and reboots.
First step is always to recreate the problem and see it in action. No problem there. Telling Windows Update to proceed resulted in precisely the described result, after a fair bit of time waiting for a frigging restore point to be created. I’d read about the failing 8.1 upgrade so I half expected it to be Microsoft’s fault, even though this machine was running Windows 7. Roger didn’t need anything from the update so worst case I thought, I’ll just disable Windows Update entirely.
First things first
Once I had confirmed that there was a problem, I begun by clearing out various crapware that was installed, mainly different kinds of toolbars and some video player that seemed to be a repackaging of VLC mainly. It’s hard to see why this software is installed or where it came from. Roger uses only Word and the browser. I figure he’s the sort that clicks on various malicious ads for some reason. At least Roger has been coerced into using Chrome instead of IE…
So I uninstall everything I don’t recognize and reboot, because rebooting is something you do a lot in Windows land… OK, maybe the update will work now without all the crap installed. It’s worth a try at least.
Initiate the update… It creates a restore point… wait… wait… wait…. Reboot. Update still fails at 30%.
Trial and error
Now the real work begins. Maybe Microsoft screwed up their patches or something? There were 5 security patches waiting to be installed so let’s try them one by one.
- First one fails.
- Second one fails.
- Everyone but the first and second one fails.
OK… Let’s just do the damn IE patches first. They also fail. And for every try, I’m forced to wait for Windows to create another damn restore point which takes several minutes. This on an almost brand new Intel NUC with an SSD.
Bored…
While waiting for the damn restore points, I am seriously considering if I can just wipe the machine and force Roger to use Linux instead. All he needs is Word. So I decide to download LibreOffice and see how their docx support is these days. Downloading 200MB takes a while on the effectively 2MBit connection. Still quicker than the now cancelled restore point. So I click through the installer, get to the progress bar, and wait. And wait. And wait.
Why the fuck isn’t the progress bar moving?
Instinctively, I open the task manager to see what the hold up is. Apparently nothing. No CPU is being used. No memory is consumed. It’s an SSD so disk speed is not an issue. Change to the services tab and same thing, nothing obvious. I try disabling the antivirus (Microsoft’s own so should be compatible right?). Good try chump, still no difference.
Second time in the task manager, I notice something though. A service which doesn’t really sound very official: safetynut. I find out where safetynut.exe lives and sure enough, it lives in something like:
C:\Program Files (x86)\Movie Toolbar\Safetynut
But I uninstalled that! Fine.. End process. To which Windows replies:
You don’t have permission to end this process
W T F
OK computer, I’m going to stop you right there. I am the administrator. I am your GOD. And as said deity, I command you to end that process!
God or no god, you still don’t have permission to do that
OK, fine, be that way. Delete C:\Program Files (x86)\Movie Toolbar\Safetynut.
Could not delete safetynut.dll as it is in use
Shaka, when the walls fell…
It’s an amazing “feature” in Windows that a program can lock a file and thus prevent you from deleting it. It’s also an amazing “feature” that the administrator can be refused the permission to do something. No recourse left but to reboot into safe mode.
To safe mode we go!
First, I go into the normal safe mode with a desktop. Still can’t delete the dll file though as it is “in use”. Time to open regedit and delete all references to safetynut from the registry. Search, delete. Rince, repeat…
Next reboot to safe mode with only a command line window. Navigate to the folder and delete the file and the folder, then reboot.
Success!
No more safetynut. Let’s try Windows Update again. Ooh, that’s a mighty fast restore point creation! And the update succeeds!
So apparently, safetynut was actively preventing Windows Update from proceeding. Roger promptly got a stern talking to about installing any software or clicking on ads/popups (I also installed adblock plus in Chrome). But it got me thinking about malware in general..
Most people are trained to install malware
In my view, none of this is the user’s fault. The fact is that Microsoft has trained everyone to install shitty software from untrusted sources. Let’s go back a few years, to the days of yore, in the time of Windows 98 and Windows 2000. If you reinstalled Windows back then, and I did a lot, then you very quickly got a routine for downloading the software you needed once Windows was installed.
First obvious things to install were the drivers for your network card, sound card and graphics card. You even possibly needed to install SATA-drivers during the actual install or the installer wouldn’t find your disk. If you did not have that on a floppy, you were screwed. But OK, you had your floppy, and you had your drivers on CD. Next you needed:
- A browser, because Internet Explorer is still a gaping security hole
- A firewall, because even up to XP, being exposed to the internet directly meant instant infection
- Antivirus, anything that wasn’t Norton would do…
- PDF-reader
- zip/rar-extractor
I’d like to draw your attention to the last item. Something so mundane as a zip-extractor was not built in to Windows. XP was the first version (if I remember correctly) to include a built in zip-extractor. This specific flaw trained everyone to download Winzip or Winrar. Quite possibly, they would resort to getting a pirated serial key as well. The problem? Now users are trained to go to any website their 10-year old neighborhood tech support kid tells them to and click Download.
Here’s a screenshot of the pirate bay to illustrate (to clarify, do NOT download your software from torrent sites. It’s just an example of this behavior). The big download buttons will lead to ads, online poker or who knows. We can be quite sure that they will lead to endless evil. On the internet, never FUCKING EVER press a big styled button with the text “Download”. The link you want is the smaller green text: “get this torrent”.

Now, assuming you managed to avoid the big download buttons to download your program, you have your completely unverified .exe file or .msi file, you double click on it, and what do you get? More fucking bullshit. Here’s a screenshot of the Winzip (totally unnecessary program today) installer. Right after you agree to the Winzip Terms of Service, you get another license agreement.
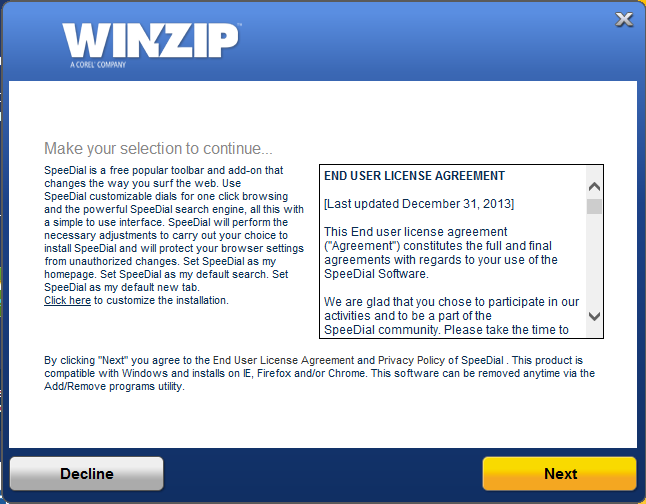
How the screaming fuck are ordinary users supposed to understand that pressing Next will lead to untold horrors and pressing Decline is the way to install the software they want? They won’t of course. That’s the whole point!
I bet this is the source of 99% of all malware on Windows. And the problem is that this is a perfectly acceptable way of getting software. Macs have the same problem to some minor extent. They are also being trained to download strange files from various pages. It is NOT accepted on Linux. The reason you don’t need antivirus on Linux is not because the system is more secure. All software is brittle and insecure. The vital difference is in how Linux users get their software.
The way it should be
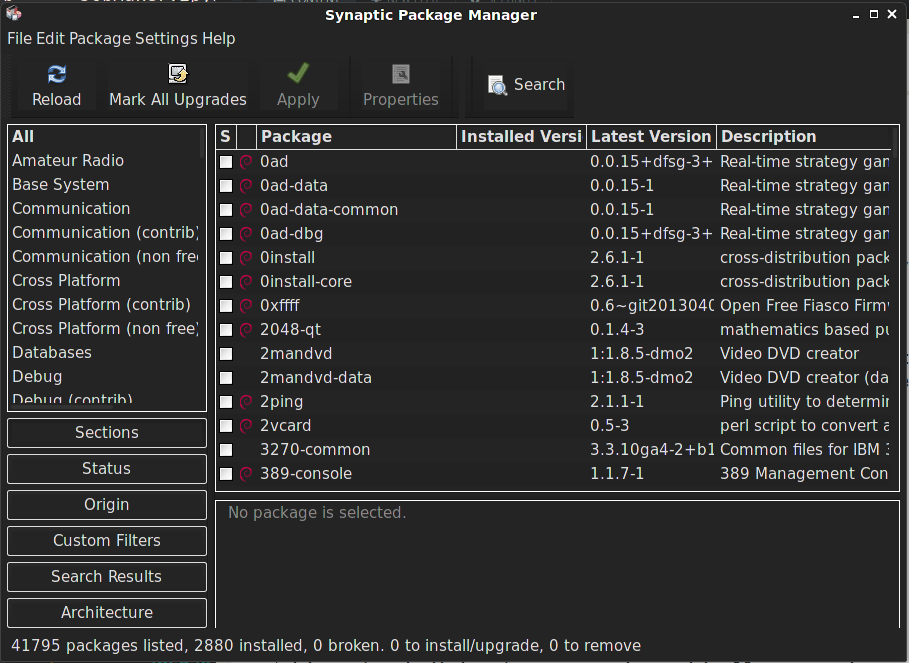
Here’s a screenshot of the package manager in Debian:
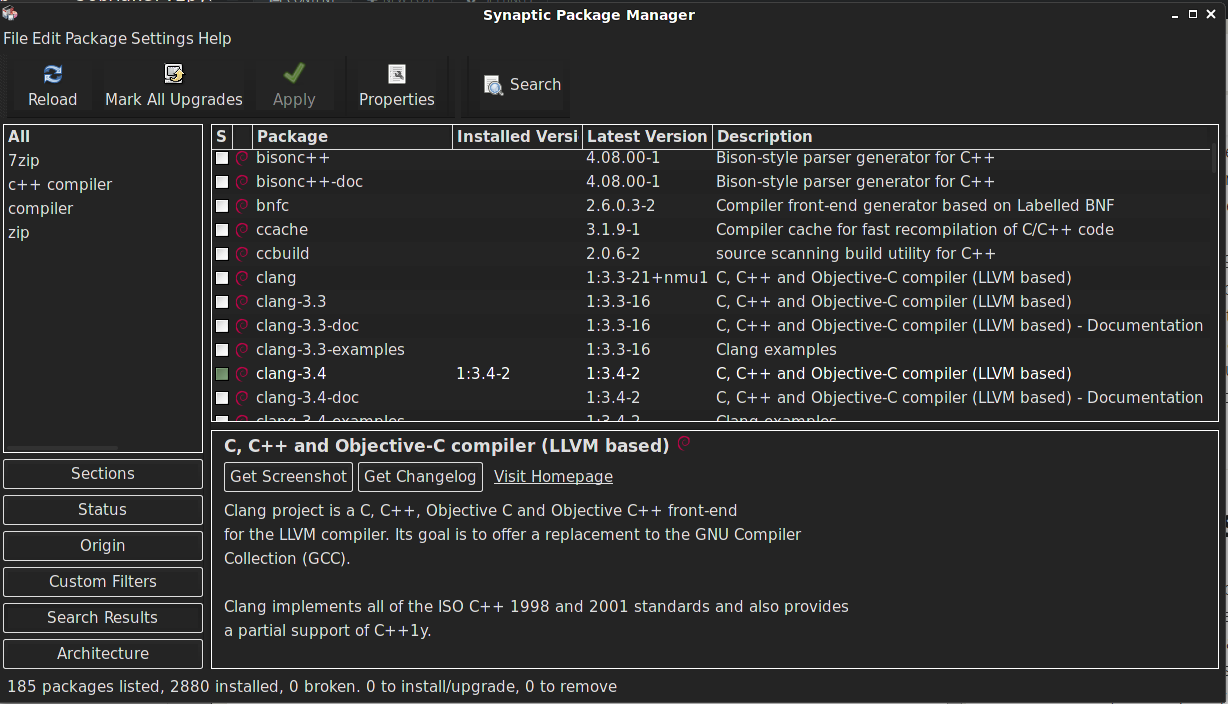
Now let’s say I need a c++ compiler and one was not installed already. I search for “c++ compiler” and there’s clang. To this day, I have no idea how I can get a compiler on Windows.
Installing 99% of all software is super easy and reliable on Linux. All of these packages have been checked by the people working on the distro. If any package were to install a toolbar or other malware, you can bet your ass that it would be removed from the official sources. And because this is how Linux users are trained to install their software, they will have some degree of suspicion against download links on unknown websites. Installing malware becomes notably harder than installing good software.
The coming app stores
Both OS X and Windows are trying to push their users to use their “app stores”. While I have many negative things to say about them, they should hopefully reduce the included malware problem and train users to only install garbage from trusted sources.